Difference between revisions of "PFSense and OPNsense"
| Line 55: | Line 55: | ||
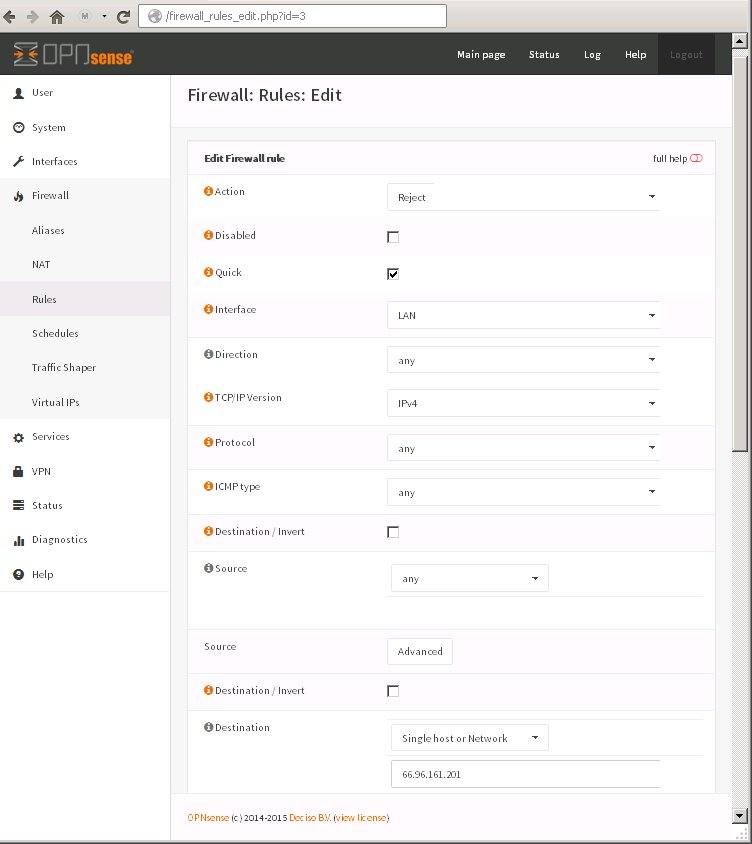
Example: Block all LAN workstations from being able to access the single IP address: 66.96.161.201 which will prevent users from being able to access a particular web site as well as any other traffic outgoing to that host. | Example: Block all LAN workstations from being able to access the single IP address: 66.96.161.201 which will prevent users from being able to access a particular web site as well as any other traffic outgoing to that host. | ||
| − | Illustration shows using OPNsense to create a RULE under the tab FLOATING. This rule once created will be visible under the LAN tab. This rule is a REJECT rule. | + | Illustration shows using OPNsense to create a RULE under the tab FLOATING. This rule once created will be visible under the LAN tab. This rule is a REJECT rule. This is a host based blocking example that does _not_ use DNS blocking. |
[[File:opnsensefirewallimage0001.jpg]] | [[File:opnsensefirewallimage0001.jpg]] | ||
Revision as of 14:15, 25 January 2016
OPNsense is a fork of PFSense. They are both nearly identical. If you consider the differences in the interfaces of the two, there is no more deviation than that of one version to the next of the same package.
OPNsense might be an excellent product, however, beyond installation there is absolutely no documentation on usage provided by the developers. It is a product without a manual. Unless you have a good background in networking concepts, firewalls, and pf (packet filter) under FreeBSD then you will likely struggle to do much beyond getting it up and running less any useful configuration.
With either PFSense or OPNsense you will be able to accomplish the same things. PFSense tends to be much better documented, however with that being said, neither are well documented. Please feel free to contribute what you have learned and use with these products here.
blocking websites
(1) via dns:
If the built in DNS Forwarder or DNS Resolver are in use, an override can be configured which will resolve the website to block to an invalid IP address.
(2) via firewall rule:
This is not a feasible solution for sites that return low TTLs and spread the load across many servers.
A hostname may be entered in a network alias, and then that alias may be applied to a block rule.
Another option is finding all of a site's IP blocks, creating an alias with those networks, and blocking traffic to those destinations.
BLOCKING DIRECTION
Consider that your machine are attempting to contact external sites as well as external hosts are trying to contact machines on your network.
(1) Stop machines from attempting to contact hosts on your network
Create rules that block connections via your WAN.
- Firewall → Rules → WAN tab and press the upper-right + button
- for Action, select Block
- check the "Quick" box which will cause the rule to take action immediately on match.
- for Interface, select WAN
- for TCP/IP Version, select IPv4
- for Protocol, select any
- for Source: (Type: Single host or alias) and (Address: enter name of the URL alias which contains the IP addresses you want to block)
- for Destination select any
- enter a Description
- Save and Apply Changes
(2) Stop hosts on your network from contacting blacklisted external hosts
To prevent hosts on your network from communicating with blacklisted hosts online you create rules that block outgoing connections from your LAN. For each alias URL and each LAN just create a new firewall rule.
- Firewall → Rules → LAN tab and press the upper-right + button
- for Action, select Reject
- check the "Quick" box which will cause the rule to take action immediately on match.
- for Interface, select LAN
- for TCP/IP Version, select IPv4
- for Protocol, select any
- for Source select any
- for Destination: (Type: select Single host or alias) and (Address: enter the name of the URL alias which contains the IP addresses you want to block)
- enter a Description
- Save and Apply Changes
Example: Block all LAN workstations from being able to access the single IP address: 66.96.161.201 which will prevent users from being able to access a particular web site as well as any other traffic outgoing to that host.
Illustration shows using OPNsense to create a RULE under the tab FLOATING. This rule once created will be visible under the LAN tab. This rule is a REJECT rule. This is a host based blocking example that does _not_ use DNS blocking.
It is also possible to block a single workstation on your LAN, or even group of workstations from accessing a single host or group of hosts online. When creating the firewall rule such as the one used in the illustration above, if you specify a "Single Host or Network" for "Source" you will block access to the one workstation on your LAN. By defining an alias you can create a group of workstation also.