Internet Security 2012 Virus
This new Rogue Antivirus malware has surfaced in 2011 and is more aggressive than predecessors like the older A-Fast Antivirus Scam. It is particularly dangerous because, even in Mozilla Firefox, it can install automatically and infect your computer. As always with Microsoft Internet Explorer, it is the most susceptible to this type of malware.
Those vulnerable tend to be individuals doing internet searches, clicking on links to unknown sites. This can be information searches or image searches. As always, those seeking pornography tend to be the most likely to encounter this malware, however, standard clipart searches on Google Images, or other standard user searches is also encountering this malware.
There are variants. The first incarnations of this Rogue Antivirus were less aggressive in that the user had to click on a pseudo button or link to install the virus. The most recent variants will automatically install, override Windows security center, and cripple the operating system by diverting the .exe (executable) file type association. The common browsers, including Microsoft Internet Explorer, Mozilla Firefox, and Google Chrome all are hijacked. The user cannot run common executable, such as the Windows Registry Editor or System Restore, and the web browsers are unable to navigate to web sites. The level of infiltration depends on the variant and how the user responds.
Internet Security 2012 is only one of the names this rogue uses. It is a name changing rogue. Some of the known variants are listed here:
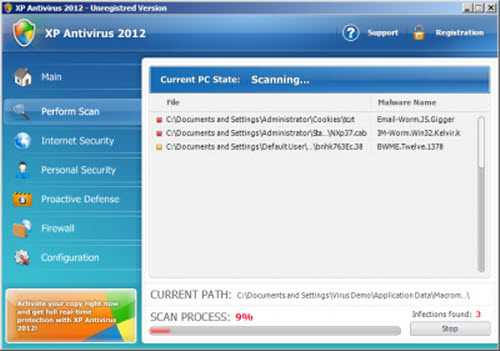
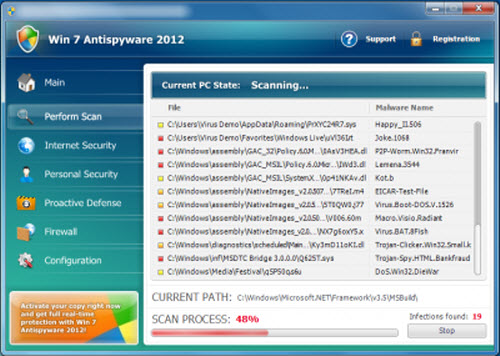
XP Antispyware 2012, Vista Antispyware 2012, Win 7 Antispyware 2012, XP Antivirus 2012, Vista Antivirus 2012, Win 7 Antivirus 2012
XP Security 2012, Vista Security 2012, Win 7 Security 2012, XP Home Security 2012, Vista Home Security 2012, Win 7 Home Security 2012, XP Internet Security 2012, Vista Internet Security 2012, Win 7 Internet Security 2012
This rogue was fist spotted in 2010 and as of the end of 2011 there are over 60 reported variants.
Contents
Pathology
Internet Security 2012 starts a pseudo scan process and then generates and shows fake messages about viruses, Trojans and worms detected on the computer. The detected viruses cannot be deleted unless the program license is purchased.
It will display the Internet Security 2012 interfaces. It typically also displays a fake Windows Security Center window which states that the computer is not protected. It promotes the rogue anti-virus applications, Internet Security 2012, or whatever variant is present. The user is prompted to register the program in order to remove the "fake" threats.
During the installation XP Antivirus 2012 copies the following files to the hard drive:
%AllUsersProfile%\Application Data\157850g1p046c522p184r5dtv4q8 %AppData%\157850g1p046c522p184r5dtv4q8 %Temp%\157850g1p046c522p184r5dtv4q8 %UserProfile%\Templates\157850g1p046c522p184r5dtv4q8 %UserProfile%\Local Settings\Application Data\%random%.exe
You will find the rogue process executable deposited in the following path:
C:\Documents and Settings\<username>\Local Settings\Application Data\
There is typically a single executable, however, the name is inconsistent but tends to be three characters in the filename before the extension. Examples of %random%.exe:
kjm.exe kdn.exe mdm.exe
Registry keys impacted
HKEY_CLASSES_ROOT\.exe\shell\open\command "(Default)" = '"%LocalAppData%\kdn.exe" -a "%1" %*' HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center "FirewallOverride" = '1' HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center "AntiVirusOverride" = '1' HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\IEXPLORE.EXE\shell\open\command "(Default)" = '"%LocalAppData%\kdn.exe" -a "C:\Program Files\Internet Explorer\iexplore.exe"' HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\FIREFOX.EXE\shell\safemode\command "(Default)" = '"%LocalAppData%\kdn.exe" -a "C:\Program Files\Mozilla Firefox\firefox.exe" -safe-mode' HKEY_LOCAL_MACHINE\SOFTWARE\Clients\StartMenuInternet\FIREFOX.EXE\shell\open\command "(Default)" = '"%LocalAppData%\kdn.exe" -a "C:\Program Files\Mozilla Firefox\firefox.exe"' HKEY_USERS\.DEFAULT\Software\Microsoft\Internet Explorer\BrowserEmulation "TLDUpdates" = '1' HKEY_CURRENT_USER\Software\Classes\exefile\shell\open\command "(Default)" = '"%LocalAppData%\kdn.exe" -a "%1" %*' HKEY_CURRENT_USER\Software\Classes\.exe\shell\open\command "(Default)" = '"%LocalAppData%\kdn.exe" -a "%1" %*' HKEY_CURRENT_USER\Software\XP Internet Security 2012 HKEY_LOCAL_MACHINE\SOFTWARE\XP Internet Security 2012 HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\XP Internet Security 2012
Removal
It is possible to remove this malware without downloading any special removal tool. It was accomplished in our lab by using tools included with Microsoft Windows XP.
- regedit.exe
- System Restore
- Task Manager
An overview of the process involved using task manager to kill the rogue process from memory, repeatedly, throughout the rest of the procedure. The process restarts every 30 seconds or so, and must continuously be killed. Using the Windows Registry editor to remove the keys above. Navigating to the Application Data folder for every user and deleting the rogue executable. Reboot. Open file type associations and create new association for exe extension as "Application". Creating a shortcut on the windows desktop to System Restore, right clicking on the shortcut, and running it as "Administrator". Restoring to a checkpoint prior to the introduction of the rogue on the system.
Our Manual Removal Process Explained in detail
Ensure the following:
- Show Hidden Files and Folders in Windows.
- Show extensions for known file types.
- Do not hide protected operating system files.
The Internet Security 2012 interface opened. It did not look like part of the web browser. It was not only showing the false virus scan interface, it was actually generating disk i/o activity. It placed an icon in the icon tray. Previously such false anti virus interfaces were actually just browser windows manipulated by javascript and css to look like a stand alone program. In this case, I was actually seeing a stand alone program. It disabled the real Windows Security Center. In task manager I could see the process kjm.exe running. I am very familiar with what processes belong in the windows task manager through experience and therefore I spotted this rogue process immediately.
We will be referring to %random%.exe as kjm.exe since that is what it was called on our lab computer. Again, it will likely have another name, made up of 3 characters, if it appears on your system.
The Internet Security 2012 interface could be killed via the task manager by killing kjm.exe. However, within 30 seconds to over a minute it would come back. kjm.exe would appear again in task manager. Although I seen kjm.exe, the process will likely have another 3 character name on another infected PC. The Internet Security 2012 interface would claim to have detected viruses. It was opening other application windows associated with anti virus.
This virus evaded the anti virus software running on the system. This virus also modified system files so that Microsoft Internet Explorer, and Firefox would not allow browsing of the Internet. The browsers would display a message warning that any web site attempting to load was a dangerous site and had to be blocked, including google.com.
Windows search failed to locate kjm.exe on the system hard disk drive.
It turned out that kjm.exe, the process for Internet Security 2012, was located in
C:\Documents and Settings\<username>\Local Settings\Application Data\kjm.exe
Running cmd.exe as user administrator opened a dos shell. Navigated to the path of the rogue executable and removed it with the del command.
del kjm.exe
Ensure the process is NOT running in task manager before attempting to delete it.
Going to My Computer, Tools, Folder Options, File Types, you need to restore exe. This may or may not be successful.
The malware virus manipulated windows file type associations so that executable programs would no longer run. Trying to run the Windows registry editor regedit.exe would display the windows file type dialog.
Since it was impossible to run System Restore after the malware manipulated file type association for exe it had to be ran via a trick as described above. (more detail needed)
You need to run the Microsoft System Restore located at the following path:
%SystemRoot%\System32\restore\rstrui.exe
Create a shortcut to this path on your desktop. Right click on the shortcut and choose to "Run as..." Run it as the Administrator user. This will circumvent the messed up exe association corruption in the registry and allow you to run system restore. Restoring to a previous checkpoint, one that you know is prior to the infection, will get you back up and running.
Additional Removal Tactics
You can use this debugged serial key 3425-814615-3990 to register the rogue application in order to stop the fake security alerts. Just click the Registration button and then select "Activate manually".
Use anti-malware software (STOPzilla) to scan and remove the virus.
Other Ways to Restore .exe Association
Copy the text in bold below and paste to Notepad.
Windows Registry Editor Version 5.00 [HKEY_CLASSES_ROOT\.exe] @="exefile" "Content Type"="application/x-msdownload"
4. Save file as fix.reg to your Desktop and double click to merge it into the windows registry.
Prevention
You should never click on anything suspicious, download, or install any third party software without knowing the source exactly. Remember, most modern virus threats involve duping the end user into thinking he or she is doing something necessary out of some threat of a virus. Visiting untrusted web sites expose you to virus threats.
- Never use Microsoft Internet Explorer
- Correct use of the NoScript plugin for Firefox
External Resources
The following online resources may be helpful to you in identification and removal of this rogue malware.
- Malware Removal Instructions
- There is a really good and very thorough instructional video on youtube. Watch this video even if you utilize another removal resource. Fake XP Internet Security 2012 Virus Removal
- It is nice to know that the authorities are actually going out and making some arrests of the criminals behind these scams. Read Report: Fake Anti-Virus "Scareware" Programs on the Decline